DOJ asked to probe whether Biden officials let Microsoft off easy in exchange for cushy jobs

Former officials in the Biden administration have been credibly accused of letting a tech giant slide on preventable cybersecurity breaches only to later secure lucrative arrangements with or cushy jobs at the same corporation.
The American Accountability Foundation, a nonprofit government oversight and research organization, asked the Justice Department in a lengthy letter on Tuesday to open a formal investigation into Microsoft and several Biden officials.
'We will act where the facts and the law support it.'
Among the Biden cronies singled out in the letter is Lisa Monaco, the former deputy attorney general whose post-government career move captured President Donald Trump's attention in September 2025.
Trump wrote that "Corrupt and Totally Trump Deranged Lisa Monaco (A purported pawn of Legal Lightweight Andrew Weissmann)" had "been shockingly hired as the President of Global Affairs for Microsoft, in a very senior role with access to Highly Sensitive Information. Monaco's having that kind of access is unacceptable, and cannot be allowed to stand. She is a menace to U.S. National Security, especially given the major contracts that Microsoft has with the United States Government."
Monaco's employment at Microsoft apparently also struck the team at AAF as potentially problematic.
The watchdog noted that Monaco — who had announced a cyber fraud initiative in 2021 aimed at using the False Claims Act against contractors who intentionally misrepresent cybersecurity risks — proved eager to bring actions against numerous companies and institutions, but never against Microsoft.
Monaco and the rest of the Biden administration's inaction against Microsoft is especially strange because the company suffered five massive cyber intrusions by foreign criminal and state-sponsored hacker groups between 2019 and 2023 that directly and adversely impacted the U.S. government.
The AAF emphasized that these intrusions "penetrated the National Nuclear Security Administration and the Departments of Treasury, State, Commerce, and Justice, as well as the National Security Council and numerous other federal agencies" and "resulted in the theft of tens of thousands of government emails, including correspondence from the U.S. Ambassador to China, the Secretary of Commerce," and other bigwigs.

One of these cyber attacks, SolarWinds, reportedly relied on the exploitation of a flaw in Microsoft's Active Directory Federation Services. The company was allegedly aware of the flaw for years but avoided patching it for fear of jeopardizing a multibillion-dollar federal cloud contract.
Former Microsoft President Brad Smith told Congress in 2021 that "there was no vulnerability in any Microsoft product or service that was exploited" in the SolarWinds attack.
While some Biden officials proved willing to assign Microsoft some blame, it was never too much or pursued as grounds for punitive action.
The Cyber Safety Review Board, an outfit established by former Homeland Security Secretary Alejandro Mayorkas, concluded that Storm-0558, a separate cyber attack executed by Beijing-linked hackers in May 2023, was enabled by a "cascade of Microsoft's avoidable errors."
Despite such recognition that it had dropped the ball, Microsoft managed to evade any meaningful reckoning.
"These facts, in our view, present squarely the kind of conduct that the Biden administration's Civil Cyber-Fraud Initiative was created to address: knowing or reckless misrepresentations by a federal contractor regarding the cybersecurity of products sold to the government," the American Accountability Foundation said in its letter. "Yet to our knowledge, no False Claims Act investigation of Microsoft's conduct has ever been opened, while other contractors whose conduct appears materially less egregious have been pursued under the same initiative."
Besides Monaco, the watchdog made a point of mentioning several other Biden administration officials, including:
- Bryan Vorndran, a former assistant director of the FBI's Cyber Division who served as the bureau's representative on the Cyber Safety Review Board. Vorndran, who the AAF said was mysteriously recused from the board's probe into the Storm-0558 attack, joined Microsoft in June 2025 as deputy chief information security officer.
- Jerry Davis, a member of the CSRB from 2022 to 2025 who participated in the board's investigation of the Storm-0558 attack. Davis was hired as a chief security adviser at Microsoft three months after the CSRB released its report faulting the company for "inadequate" security culture.
- Robert Joyce, the former director of cybersecurity at the National Security Agency and an inaugural member of the CSRB. After leaving the NSA in 2024, he founded a cybersecurity firm that the AAF suggested counts Microsoft as one of its clients.
The AAF stressed that "federal ethics rules prohibit government officials from participating in matters in which they have a financial interest, and require cooling-off periods before certain officials may represent private parties before their former agencies."
While the AAF did not "allege that any individual violated any specific law or regulation," the watchdog noted that an investigation into the matter is warranted.
A Justice Department spokesperson told Breitbart, "The Department of Justice is committed to aggressively fighting fraud and protecting taxpayer dollars. We welcome referrals from anyone with credible information about fraud, and we will act where the facts and the law support it."
Like Blaze News? Bypass the censors, sign up for our newsletters, and get stories like this direct to your inbox. Sign up here!

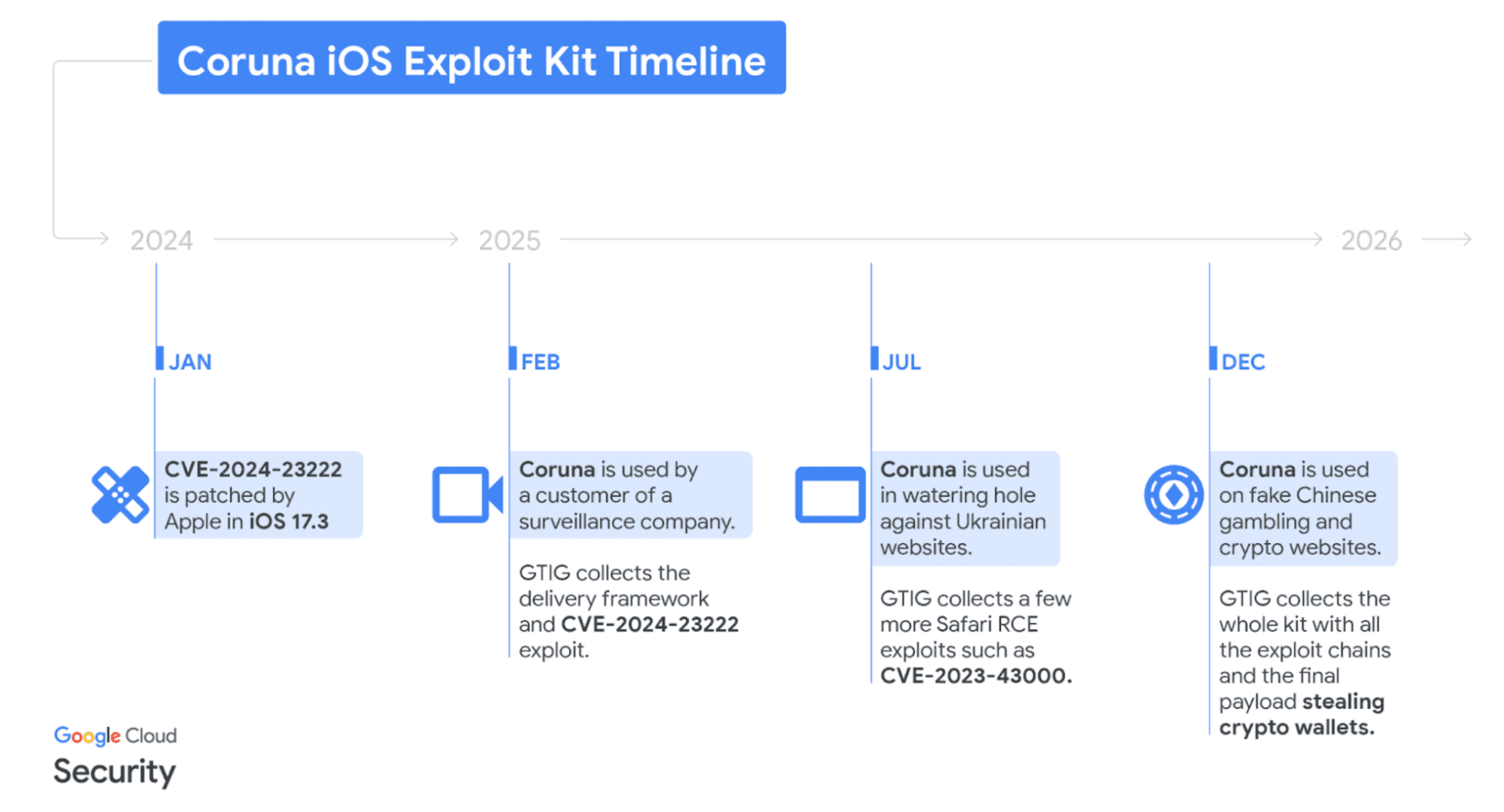 Image credit: Google
Image credit: Google Photo by Matt Cardy/Getty Images
Photo by Matt Cardy/Getty Images
 Photo by Joe Schildhorn/Patrick McMullan via Getty Images
Photo by Joe Schildhorn/Patrick McMullan via Getty Images
 Photo by Wang Gang/VCG via Getty Images
Photo by Wang Gang/VCG via Getty Images
 Muneeb Akhter. Photo by Evelyn Hockstein/Washington Post via Getty Images
Muneeb Akhter. Photo by Evelyn Hockstein/Washington Post via Getty Images

 Photo by Samuel Boivin/NurPhoto via Getty Images
Photo by Samuel Boivin/NurPhoto via Getty Images
 Bloomberg/Getty Images
Bloomberg/Getty Images The Trump administration must take decisive action to hold the Chinese government and its affiliated hackers accountable for their cyber activities.
The Trump administration must take decisive action to hold the Chinese government and its affiliated hackers accountable for their cyber activities.