Epstein files were allegedly compromised by foreign hacker in 2023; FBI admits 'cyber incident'

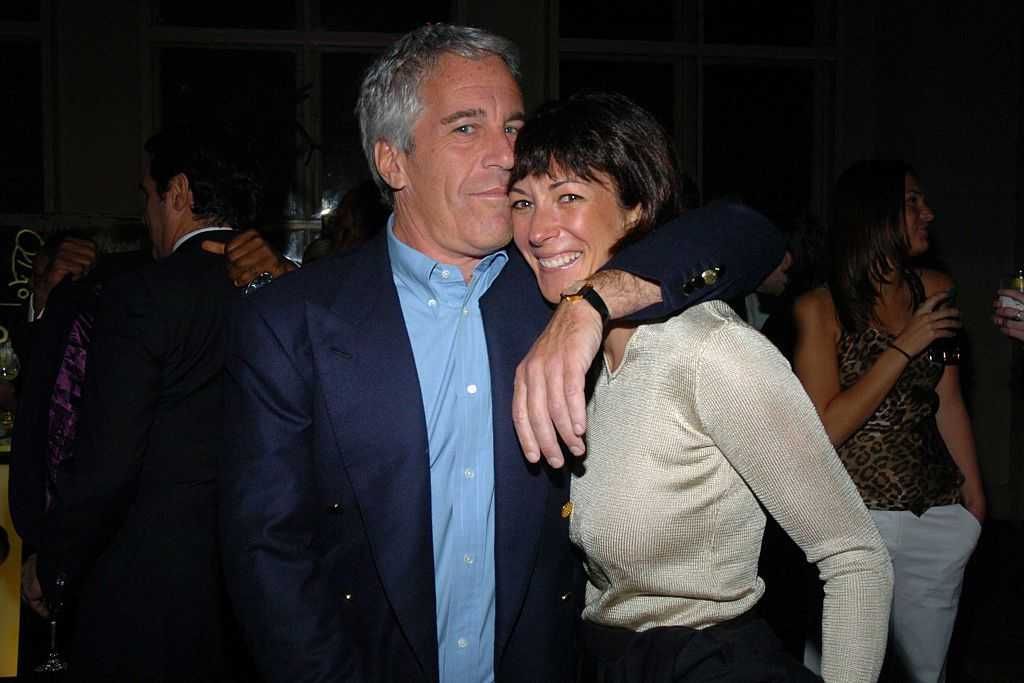
The FBI Field Office in New York produced myriad documents pertaining to its criminal probe into child sex offender Jeffrey Epstein. Attorney General Pam Bondi suggested in a Feb. 17, 2025, letter to FBI Director Kash Patel that "thousands of pages of documents related to the investigation and indictment of Epstein" were stored on site there.
Some of these documents were allegedly compromised in a hack years before the Department of Justice began publishing the heavily redacted Epstein files.
Reuters' source suggested that the hack appears to have been executed by a 'cybercriminal' rather than a foreign government.
The bureau revealed in 2023 that it was investigating a hack of its computer network, which it characterized as an "isolated incident that has been contained."
Multiple sources briefed on the matter told CNN at the time that FBI officials suspected the incident involved a bureau computer system used in the investigations of images of child sexual exploitation.
Reuters, citing a source familiar with the matter and recently published DOJ documents, reported on Wednesday that the hack entailed a foreign actor's targeting of files related to the FBI's investigation of Epstein.
The hack reportedly took place after a server at the New York FBI office's Child Exploitation Forensic Lab was allegedly left exposed by Special Agent Aaron Spivack, who did not return Reuters' numerous requests for comment but has previously issued a voluminous statement on the matter.
Among the Epstein files released by the Department of Justice in recent months is a 2024 statement from Spivack in which he addresses the allegations that he "improperly stored digital evidence at his residence"; "improperly handled, documented, and stored digital evidence and failed to secure [child sexual abuse material] within policy, resulting in a cyber intrusion"; and "exceeded the limits of his authority by contracting an outside company to develop computer software on behalf of the FBI."
Spivack — who apparently participated in the Epstein investigation — stated that the cyber "intrusion" happened on Feb. 12, 2023.
After logging into his computer to find a .txt file indicating that his network had been compromised, Spivack claimed that he ran an anti-virus sweep, which identified a potential threat. He said that he was unable, however, to remove the threat, as his "administrative privileges had been removed."
Spivack notified some of his colleagues, attempting to rectify the issue, then noticed that the main server was down, that other servers were malfunctioning, and that "the folders that contain our data was missing."
According to Spivack's timeline, he and others later noticed "strange IP activity that took place [on Feb. 12] from two IP addresses."
"The activity included combing through certain files pertaining to the Epstein investigation," stated Spivack.
It's unclear what particular files were accessed and whether they were downloaded, reported Reuters.
By 5 p.m. on Feb. 13, 2023, Spivack said, "we realized we were hacked."
The FBI reiterated that the "cyber incident" was an "isolated one" and said in a statement obtained by Reuters that "the FBI restricted access to the malicious actor and rectified the network. The investigation remains ongoing, so we do not have further comments to provide at this time."
The FBI did not immediately respond to a request for comment from Blaze News.
Reuters' source suggested:
- that the hack appears to have been executed by a "cybercriminal" rather than a foreign government;
- that the hacker did not appear to realize he or she had hacked a law enforcement server; and
- that the hacker expressed revulsion at the presence of child sexual abuse images on the device and threatened to turn its owner over to the FBI.
The hacker — whom the FBI allegedly spoke to on video chat but was unable to identify or locate — may have acted alone, but Jon Lindsay, an associate professor at the Georgia Institute of Technology's School of Cybersecurity and Privacy, suggested that the hack demonstrates the files' potential intelligence value.
"Who wouldn’t be going after the Epstein files if you’re the Russians or somebody interested in kompromat?" Lindsay told Reuters. "If foreign intelligence agencies are not thinking seriously about the Epstein files as a target, then I would be shocked."
Reuters indicated it was unable to "establish the result of the bureau's internal investigation" regarding Spivack or connect with FBI agents identified in the documents as being involved in the investigation.
Spivack stressed in his 2024 statement, "I have rescued more exploited children than anyone in the NYFO and in most of the Bureau. All I wanted to do was to better the Bureau. I did not know how to do everything right, but I always did the right thing and everything I did was with good intentions. I love this job. I was not reckless."
Like Blaze News? Bypass the censors, sign up for our newsletters, and get stories like this direct to your inbox. Sign up here!

 Photo by Roberto Schmidt/Getty Images
Photo by Roberto Schmidt/Getty Images Photo by Roberto Schmidt/Getty Images
Photo by Roberto Schmidt/Getty Images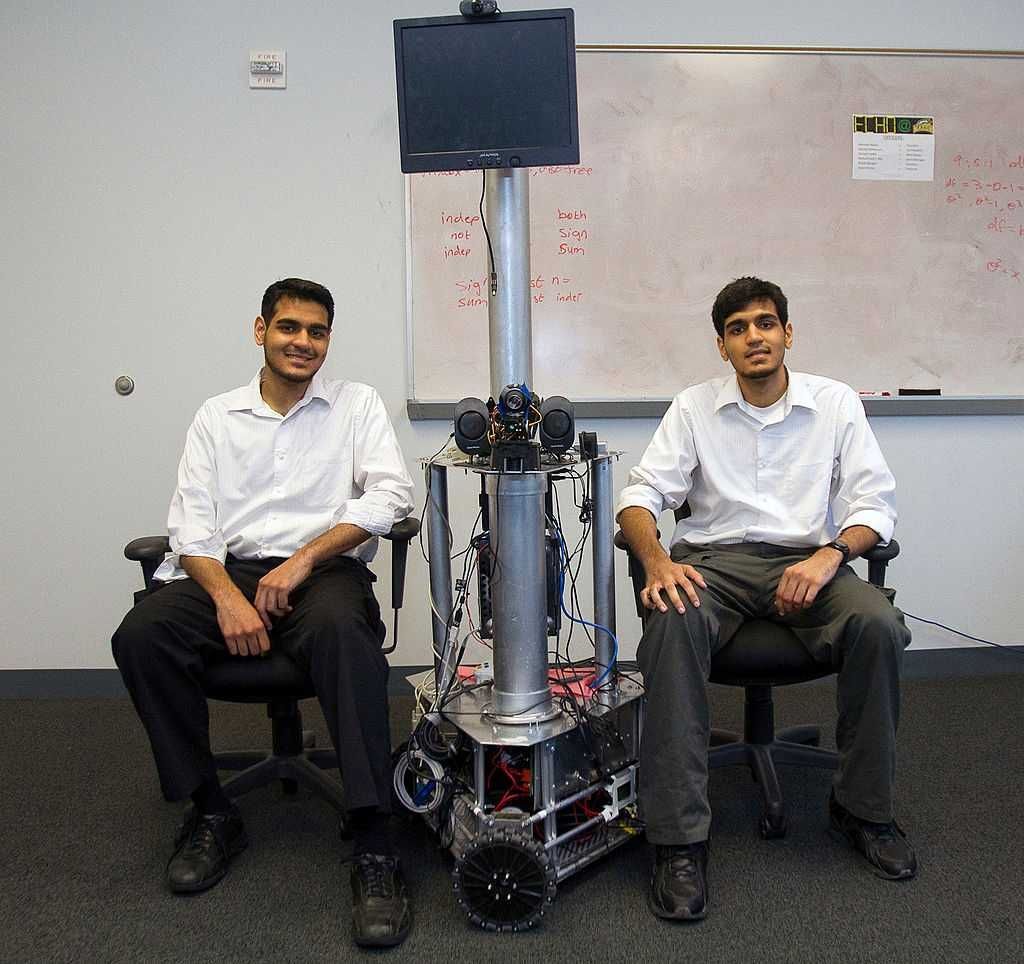
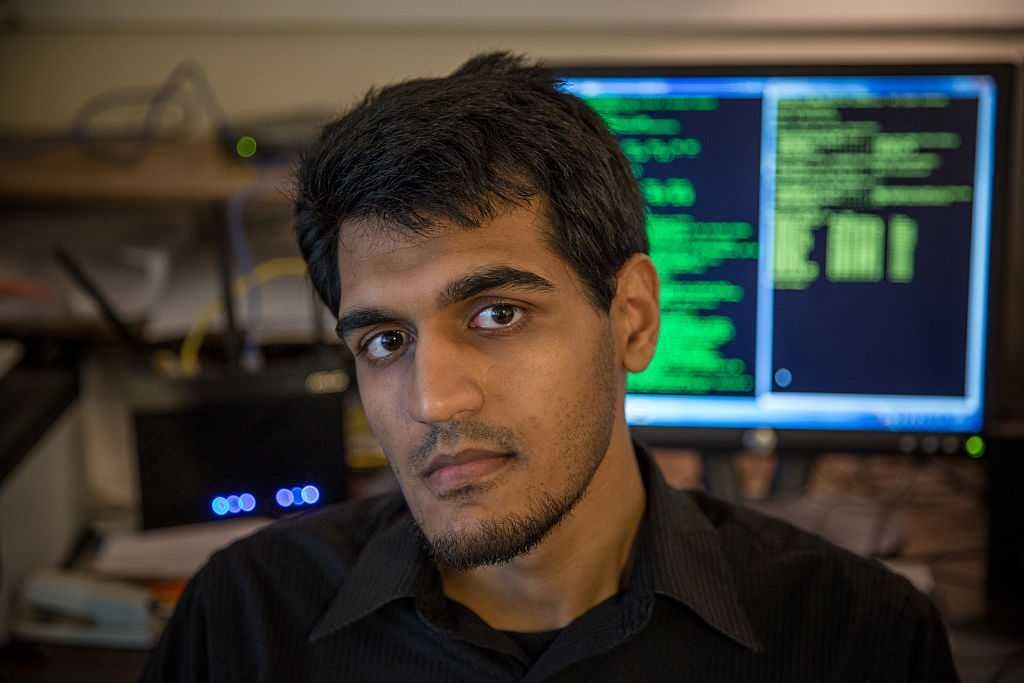 Muneeb Akhter. Photo by Evelyn Hockstein/Washington Post via Getty Images
Muneeb Akhter. Photo by Evelyn Hockstein/Washington Post via Getty Images The press that lied about Russia is not backing off after seeing the Durham Annex. Instead is in denial or looking for a new spin.
The press that lied about Russia is not backing off after seeing the Durham Annex. Instead is in denial or looking for a new spin.
 Missile launch station in Cold War-era underground bunker, Minuteman Missile National Historic Site, South Dakota. Photo by: Education Images/Universal Images Group via Getty Images
Missile launch station in Cold War-era underground bunker, Minuteman Missile National Historic Site, South Dakota. Photo by: Education Images/Universal Images Group via Getty Images First thermonuclear test on October 31, 1952. Photograph on display in the Bradbury Science Museum, photo copied by Joe Raedle
First thermonuclear test on October 31, 1952. Photograph on display in the Bradbury Science Museum, photo copied by Joe Raedle
 Former first lady Michelle Obama joins Elmo for an announcement in 2013. Photo by Win McNamee/Getty Images
Former first lady Michelle Obama joins Elmo for an announcement in 2013. Photo by Win McNamee/Getty Images
 Photo Illustration by Budrul Chukrut/SOPA Images/LightRocket via Getty Images
Photo Illustration by Budrul Chukrut/SOPA Images/LightRocket via Getty Images  Feature China/Future Publishing via Getty Images
Feature China/Future Publishing via Getty Images